Guide To Network Security Review Answers
Now in its third edition, the best-selling SECURITY+ GUIDE TO NETWORK SECURITY FUNDAMENTALS provides the most up-to-date industry information, reflecting the changes in security that have occurred since the most recent CompTIA Security+ objectives were created. The book covers all of the new CompTIA Security+ 2008 exam objectives and maps to the new Security+ 2008 exam.
- Security+ Guide To Network Security Fundamentals 4th Edition Review Questions Answers
- Networks Answer Key
Th Now in its third edition, the best-selling SECURITY+ GUIDE TO NETWORK SECURITY FUNDAMENTALS provides the most up-to-date industry information, reflecting the changes in security that have occurred since the most recent CompTIA Security+ objectives were created. The book covers all of the new CompTIA Security+ 2008 exam objectives and maps to the new Security+ 2008 exam. This updated edition features many all-new topics, including topics new to the CompTIA exams like cross site scripting, SQL injection, rootkits, and virtualization, as well as topics of increasing importance in the industry as a whole, like the latest breeds of attackers, Wi-Fi Protected Access 2, and Microsoft Windows Vista security.
The fourth edition of Principles of Information Security explores the field of information security and assurance with updated content including new innovations in technology and methodologies. Readers will revel in the comprehensive coverage that includes a historical overview of information security, discussions on risk management and security technology, current certification information, and more. The text builds on internationally recognized standards and bodies of knowledge to provide the knowledge and skills students need for their future roles as business decision-makers. Information security in the modern organization is a management issue which technology alone cannot answer; it is a problem that has important economic consequences for which management will be held accountable. Readers can feel confident that they are using a standards-based, content-driven resource to prepare for their work in the field. PART OF THE NEW JONES & BARTLETT LEARNING INFORMATION SYSTEMS SECURITY & ASSURANCE SERIES!The study of information system security concepts and domains is an essential part of the education of computer science students and professionals alike. Security Policies and Implementation Issues offers a comprehensive, end-to-end view of information security policies and frameworks from the raw organizational mechanics of building to the psychology of implementation.
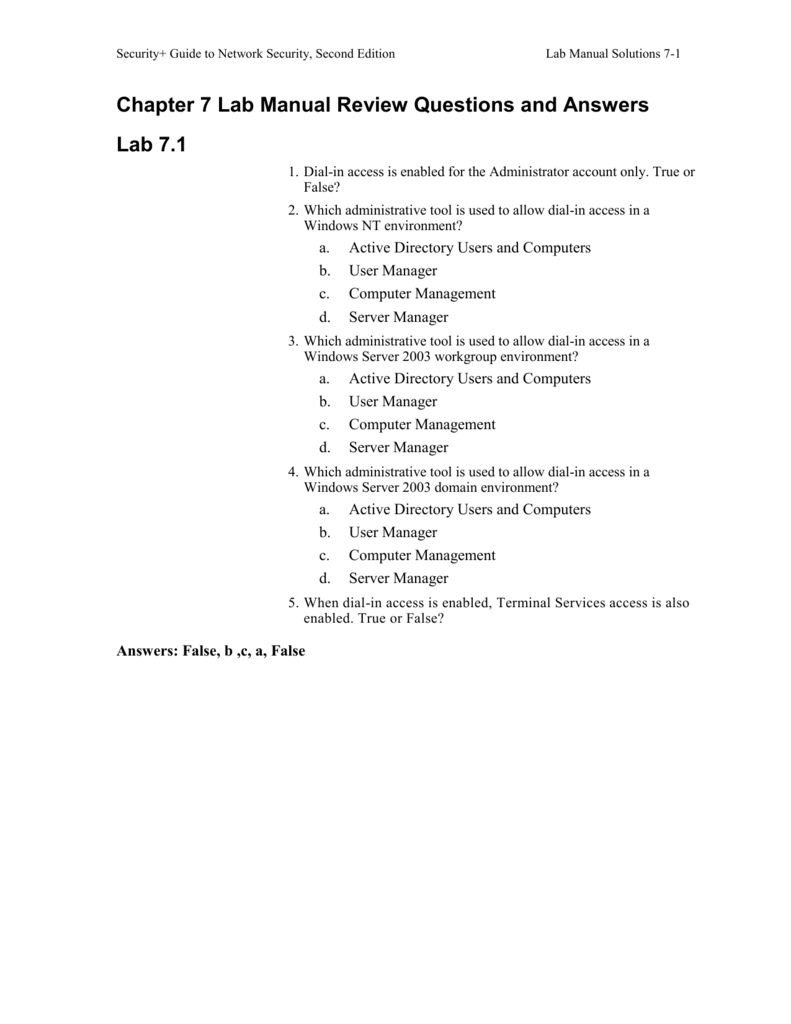
Security+ Guide to Network Security Fundamentals (Cyber Security) by Mark Ciampa. Format: Paperback Change. I would have given 5 except for the inexcusable lack of answers/explanations to the end of chapter review questions, the lack of answers/explanations to the Certblaster practice exams, and the insane price. 4.0 out of 5 stars. Security+ Guide to Network Security, Second Edition Lab Manual Solutions 4. Chapter 4 Lab Manual Review Questions and Answers.
It presents an effective balance between technical knowledge and soft skills, and introduces many different concepts of information security in clear simple terms such as governance, regulator mandates, business drivers, legal considerations, and much more. With step-by-step examples and real-world exercises, this book is a must-have resource for students, security officers, auditors, and risk leaders looking to fully understand the process of implementing successful sets of security policies and frameworks. Reflecting the latest developments from the information security field, best-selling Security+ Guide to Network Security Fundamentals, 4e provides the most current coverage available while thoroughly preparing readers for the CompTIA Security+ SY0-301 certification exam.
Its comprehensive introduction to practical network and computer security covers all of the the new CompTIA Security+ exam objectives. Cutting-edge coverage of the new edition includes virtualization, mobile devices, and other trends, as well as new topics such as psychological approaches to social engineering attacks, Web application attacks, penetration testing, data loss prevention, cloud computing security, and application programming development security. The highly successful security book returns with a new edition, completely updated Web applications are the front door to most organizations, exposing them to attacks that may disclose personal information, execute fraudulent transactions, or compromise ordinary users. This practical book has been completely updated and revised to discuss the latest step-by-step techniques for attacking and defending the range of ever-evolving web applications. You'll explore the various new technologies employed in web applications that have appeared since the first edition and review the new attack techniques that have been developed, particularly in relation to the client side.
OFFICIAL CERTIFIED ETHICAL HACKER REVIEW GUIDE: FOR VERSION 7.1 is a valuable resource to help you pursue the most recognized, respected hacking certification in the world. As experienced instructors of the International Council of Electronic Commerce Consultants (EC-Council), the authors draw on firsthand experience training top-caliber information security professionals for success on the council's Certified Ethical Hacker (CEH) exam. Sybex is now the official publisher for Certified Wireless Network Professional, the certifying vendor for the CWSP program.
This guide covers all exam objectives, including WLAN discovery techniques, intrusion and attack techniques, 802.11 protocol analysis. Wireless intrusion-prevention systems implementation, layer 2 and 3 VPNs used over 802.11 networks, and managed endpoint security systems. It also covers enterprise/SMB/SOHO/Public-Network Security design models and security solution implementation, building robust security networks, wireless LAN management systems, and much more. Master the skills necessary to launch and complete a successful computer investigation with the updated fourth edition of this popular book, GUIDE TO COMPUTER FORENSICS AND INVESTIGATIONS. This resource guides readers through conducting a high-tech investigation, from acquiring digital evidence to reporting its findings. Updated coverage includes new software and technologies as well as up-to-date reference sections, and content includes how to set up a forensics lab, how to acquire the proper and necessary tools, and how to conduct the investigation and subsequent digital analysis.
It is appropriate for students new to the field, or as a refresher and technology update for professionals in law enforcement, investigations, or computer security. The book features free downloads of the latest forensic software, so readers can become familiar with the tools of the trade. The classic book The Art of War (or as it is sometimes translated, The Art of Strategy) by Sun Tzu is often used to illustrate principles that can apply to the management of business environments. The Art of War for Security Managers is the first book to apply the time-honored principles of Sun Tzu's theories of conflict to contemporary organizational security. Corporate leaders have a responsibility to make rational choices that maximize return on investment.
The author posits that while conflict is inevitable, it need not be costly. The result is an efficient framework for understanding and dealing with conflict while minimizing costly protracted battles, focusing specifically on the crucial tasks a security manager must carry out in a 21st century organization. Includes an appendix with job aids the security manager can use in day-to-day workplace situations.
Provides readers with a framework for adapting Sun Tzu's theories of conflict within their own organizations. From an author who routinely packs the room at his conference presentations. Many of us, especially since 9/11, have become personally concerned about issues of security, and this is no surprise. Security is near the top of government and corporate agendas around the globe. Security-related stories appear on the front page everyday. How well though, do any of us truly understand what achieving real security involves? In Beyond Fear, Bruce Schneier invites us to take a critical look at not just the threats to our security, but the ways in which we're encouraged to think about security by law enforcement agencies, businesses of all shapes and sizes, and our national governments and militaries.
Schneier believes we all can and should be better security consumers, and that the trade-offs we make in the name of security - in terms of cash outlays, taxes, inconvenience, and diminished freedoms - should be part of an ongoing negotiation in our personal, professional, and civic lives, and the subject of an open and informed national discussion. With a well-deserved reputation for original and sometimes iconoclastic thought, Schneier has a lot to say that is provocative, counter-intuitive, and just plain good sense.
He explains in detail, for example, why we need to design security systems that don't just work well, but fail well, and why secrecy on the part of government often undermines security. He also believes, for instance, that national ID cards are an exceptionally bad idea: technically unsound, and even destructive of security. And, contrary to a lot of current nay-sayers, he thinks online shopping is fundamentally safe, and that many of the new airline security measure (though by no means all) are actually quite effective. A skeptic of much that's promised by highly touted technologies like biometrics, Schneier is also a refreshingly positive, problem-solving force in the often self-dramatizing and fear-mongering world of security pundits.
Schneier helps the reader to understand the issues at stake, and how to best come to one's own conclusions, including the vast infrastructure we already have in place, and the vaster systems-some useful, others useless or worse-that we're being asked to submit to and pay for. Bruce Schneier is the author of seven books, including Applied Cryptography (which Wired called 'the one book the National Security Agency wanted never to be published') and Secrets and Lies (described in Fortune as 'startlingly lively.¦a jewel box of little surprises you can actually use.' He is also Founder and Chief Technology Officer of Counterpane Internet Security, Inc., and publishes Crypto-Gram, one of the most widely read newsletters in the field of online security. 'The book you are about to read will arm you with the knowledge you need to defend your network from attackers-both the obvious and the not so obvious. If you are new to network security, don't put this book back on the shelf!
This is a great book for beginners and I wish I had access to it many years ago. If you've learned the basics of TCP/IP protocols and run an open source or commercial IDS, you may be asking 'What's next?' If so, this book is for you.'
-Ron Gula, founder and CTO, Tenable Network Security, from the Foreword 'Richard Bejtlich has a good perspective on Internet security-one that is orderly and practical at the same time. He keeps readers grounded and addresses the fundamentals in an accessible way.'

-Marcus Ranum, TruSecure 'This book is not about security or network monitoring: It's about both, and in reality these are two aspects of the same problem. You can easily find people who are security experts or network monitors, but this book explains how to master both topics.' -Luca Deri, ntop.org 'This book will enable security professionals of all skill sets to improve their understanding of what it takes to set up, maintain, and utilize a successful network intrusion detection strategy.' -Kirby Kuehl, Cisco Systems Every network can be compromised.
There are too many systems, offering too many services, running too many flawed applications. No amount of careful coding, patch management, or access control can keep out every attacker. If prevention eventually fails, how do you prepare for the intrusions that will eventually happen? Network security monitoring (NSM) equips security staff to deal with the inevitable consequences of too few resources and too many responsibilities. NSM collects the data needed to generate better assessment, detection, and response processes-resulting in decreased impact from unauthorized activities. In The Tao of Network Security Monitoring, Richard Bejtlich explores the products, people, and processes that implement the NSM model.
Security+ Guide To Network Security Fundamentals 4th Edition Review Questions Answers
By focusing on case studies and the application of open source tools, he helps you gain hands-on knowledge of how to better defend networks and how to mitigate damage from security incidents. Inside, you will find in-depth information on the following areas. The NSM operational framework and deployment considerations. How to use a variety of open-source tools-including Sguil, Argus, and Ethereal-to mine network traffic for full content, session, statistical, and alert data.
Networks Answer Key
Best practices for conducting emergency NSM in an incident response scenario, evaluating monitoring vendors, and deploying an NSM architecture. Developing and applying knowledge of weapons, tactics, telecommunications, system administration, scripting, and programming for NSM. The best tools for generating arbitrary packets, exploiting flaws, manipulating traffic, and conducting reconnaissance. Whether you are new to network intrusion detection and incident response, or a computer-security veteran, this book will enable you to quickly develop and apply the skills needed to detect, prevent, and respond to new and emerging threats.